Kiwi Holiday.7z Site
Use reputable tools like Malwarebytes or Microsoft Defender to run a full system scan.
Security researchers have linked "Kiwi holiday.7z" to the (also known as Thallium or Black Banshee) threat group. This group frequently uses lures related to South Korean or regional interests to distribute malware.
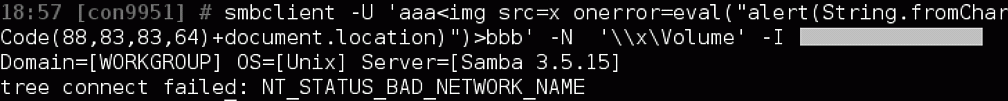
Once the user extracts the .7z archive and runs the contained files, the malware establishes persistence on the host machine and begins communicating with a Command and Control (C2) server to upload stolen data. Recent Security Context for 7-Zip Files Kiwi holiday.7z
This archive typically contains a KiwiStealer payload, a file-stealing malware designed to exfiltrate system information and specific sensitive documents.
It is usually distributed via spear-phishing emails . The file name is designed to look like a harmless travel itinerary or holiday plan to trick recipients into opening it. Use reputable tools like Malwarebytes or Microsoft Defender
The use of .7z archives for malware has surged recently due to specific vulnerabilities in the 7-Zip software itself:
If you have encountered this file or recently downloaded 7-Zip from an unofficial source, take these steps: Once the user extracts the
Look for unrecognized processes such as uhero.exe or hero.exe in your Task Manager, which are common indicators of a compromised installer. 7zip Malware: Beware 7zip.com